As we count down to Open Mainframe Summit 2022, hosted virtually and in-person in Philadelphia, PA on September 21-22, we are looking back at some of our favorite presentations from last year’s Summit.
In his Open Mainframe Summit 2021 session, Steve Winslow, Counsel at Boston Technology Law, PLLC and an open source advocate and thought leader, presented a keynote titled, “Walking the Open Source Trail Towards Supply Chain Integrity and Security.” If you missed it, watch the video or read the recap below:
Last year, Steve Winslow went on vacation to western Massachusetts. He went for a hike, where he was surprised to find the Open Source Trail.
In his talk at the Open Mainframe Summit, Steve uses this Open Source Trail as an analogy for the path that companies follow for development. He also talks about how the open-source community is working to improve security and transparency for software development.
In this summary of Steve’s talk, you’ll learn how your company can improve supply chain integrity and security by following the Open Source Trail. We’ll discuss the recommended processes for developing, delivering, and procuring open-source tools.
Starting Down the Open Source Trail
When companies first start proactively using open source, they find a pretty well-marked trail. They have quite a bit of clarity on the advantages of using open-source applications.

However, after a little while the trail starts getting a bit treacherous. Just like hikers, companies find it difficult to stay on the path. They learn the importance of
- open-source licensing,
- security considerations, and
- the dependencies that a given software has.
How Does Supply Chain Come Into the Picture?
When companies hear about publicized security vulnerabilities, the path gets more difficult. They find themselves asking questions about the software they’re using. Finally, they ask: how do we trust our supply chain? Naturally, instead of trusting that their software is secure, they ask: what more can we do to know that the software is secure?
All these questions lead us to the topic of supply chain integrity and security.
Supply Chain Integrity and Security
After quite a few well-known breaches happened in 2021, the US government established guidelines for its own software procurement. A big piece of this is the idea of a software bill of materials (SBOM). It’s an ingredients list of what makes up software. Companies should also follow a similar approach. However, for companies that are receiving third-party software, this can get a bit overwhelming.
Fortunately, we can solve supply chain security matters using the same model that open-source communities follow: create trust by building things openly. We should collaborate with others, learn from each other, and figure out the best practices.
Working as a Community to Proactively Improve Supply Chain Integrity and Security
Currently, the Linux Foundation and several other companies are following a set of processes that we’ll discuss in detail.
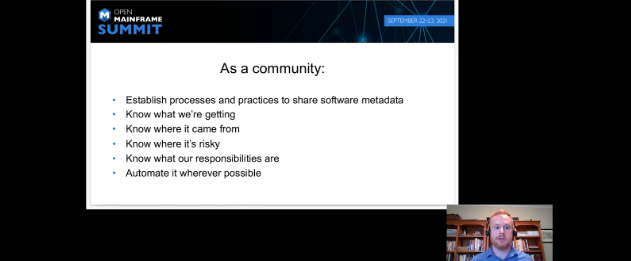
Through these practices, we can continue to build the Open Source Trail together transparently and collaboratively. Let’s get to it.
Establish Practices to Share Software Metadata
The first step to improving supply chain security and integrity is establishing practices to share software metadata. Steve talks about two major projects:
- The Software Package Data Exchange (SPDX) defines what’s in the software and contains information on dependencies, packages, and licensing of the components.
- The Open Chain Project defines a standard at the business process level. Using this standard, companies can certify how they got the proper compliance processes in place.
Both of these projects became official ISO standards.
Know What Software You’re Getting
The next step is to know in detail about the software that we are getting. Steve talks about
- The OSS Review Toolkit, which we can use it to understand, analyze, and report on the contents of a package of software and its dependencies; and
- TERN, a tool focused on container technologies that looks at the container and understands the different layers of containers underneath and what’s inside those containers.
Know Where Your Software Came From
The third step is knowing where your software comes from. Two important tools that help with this are
- Sigstore, which is used for signing software and verifying signatures in an automated manner; and
- In-toto, a tool that records and attests to metadata about the particular steps that were taken while a certain software was developed.
Know What Risks a Software Has
This step is important since our aim is to improve the security of our software. Steve discusses two projects that can help you identify risk in open-source software:
- the Open Source Security Foundation, whose community members work together on approaches to improvising security throughout the entire open-source ecosystem
- the Chaoss Community, which is focused on creating standards and tools for measuring different metrics of the project’s overall health
Know What Your Responsibilities Are
Companies are responsible for knowing about the licensing and standards of the third-party software that they’re using. There’s a wide variety of tools for scanning software for relevant license-related statements. You should choose the ones that suit your needs.
Automate Your Processes Wherever Possible
The last step to improving your supply chain security and integrity is using the relevant tools to automate your processes wherever possible. At the same time, we need human intervention as well for analyzing and implementing the practices.
Key Takeaways
Steve recommends looking at your organization and understanding where it fits in the supply chain. Know what software you are using and providing. Once you understand that, look at how your company receives, creates, and delivers software. Pull different tools to address different gaps and build a solution that works for your business. Start making small improvements, and you’ll soon get better with time. Steve concludes the session by asking us to contribute and work together with the open-source community so that we can get better together.
This has been recap of a session from Open Mainframe Summit 2021. If you’d like to learn more about Open Mainframe Summit 2022, hosted in Philadelphia, PA on September 21-22, please click here: https://events.linuxfoundation.org/open-mainframe-summit/ .
This post was written by Arnab Roy Chowdhury. Arnab is a UI developer by profession and a blogging enthusiast. He has strong expertise in the latest UI/UX trends, project methodologies, testing, and scripting.
